Safeguarding protected health information (PHI) is vital for healthcare institutions worldwide. PHI, which encompasses a broad spectrum of data from medical records to financial information related to healthcare, remains a prime target for cybercriminals. The integrity and confidentiality of this information are not only critical for compliance with privacy laws but are fundamental to maintaining […]
News
Strengthen your passwords with NIST guidelines
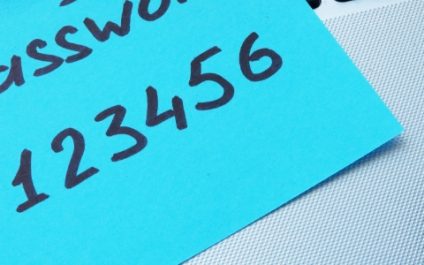
Many users unknowingly create weak passwords or mishandle them through common habits, leaving their data and accounts vulnerable to breaches. To combat this vulnerability, the National Institute of Standards and Technology (NIST) offers clear guidelines for crafting strong passwords and good practices to ensure password integrity. What is NIST? NIST is a US government agency […]
Picking the right laptop for remote work

Struggling to choose the right laptop for remote work? You’re not alone! With so many options on the market, picking a laptop can feel like a confusing maze. But don’t worry, we’ll simplify the selection process by highlighting the essential features you need to consider in order to ensure a smooth and productive workflow, wherever […]
Level up your security with biometric authentication

With passwords alone becoming more and more insufficient to ward off sophisticated cyberattacks, biometric authentication offers a more secure and convenient alternative. This innovative technology scans for a person’s distinctive physical characteristics, such as fingerprints, to verify their identity before granting them access to devices and accounts. In this blog, we take a look at […]
Unleash your team’s potential: Strategies for boosted efficiency

In the bustling world of business, the tick-tock of the clock is often the background beat. Every minute counts, and to flourish, small-business owners like you need a workforce that thrives on efficiency. With the right approach, you can transform your team into a well-oiled productivity machine, driving your business forward and helping you achieve […]
Top 5 gateways and vulnerabilities that lead to security breaches

IT-forward businesses operate more efficiently and precisely than ever before, but if they’re not taking the necessary precautions, they can also be vulnerable to more cyberattacks. With more devices connected to the internet today, it’s essential to be aware of the most common weak points that hackers use to breach your systems. Social engineering Social […]
Microsoft Edge: Your strategic partner for a secure and productive workforce

Modern businesses require tools that deliver more than basic web navigation. Microsoft Edge transcends traditional browsers, providing features that enhance productivity, streamline collaboration, and prioritize data security, ultimately propelling your business forward. Read the article below to learn five ways by which Edge improves productivity. Streamlined productivity Hub Edge’s Collections feature allows you to curate […]
Virtualization and cloud computing: Key concepts explained

Virtualization and cloud computing might seem interchangeable, but they’re not. This article explores how virtualization acts as the building block, creating simulated environments, while cloud computing leverages those environments to deliver on-demand services. Read on to learn more about the intricate relationship between these technologies and how they’re revolutionizing the future of computing. What’s the […]
From paper charts to digital data: Is transitioning to EHRs a smart move?

The healthcare industry has come a long way from paper charts to electronic health records (EHRs). While some healthcare providers have fully embraced the transition, others are still reluctant to make the move. But with the increasing use of technology in all aspects of our lives, is transitioning to EHRs really a smart move for […]
Is it worth monitoring employees online?

The digitization of the workplace has opened up new frontiers for employer oversight. With workers more connected than ever through computers and internet-based tools, companies are exploring the advantages of monitoring for optimizing workflow and enhancing productivity. Yet, this digital vigilance prompts a crucial discussion about where to draw the line between legitimate business interests […]



